Art and science of psychological operations: case studies of military application, volume two. - General Military History - Ike Skelton Combined Arms Research Library (CARL) Digital Library
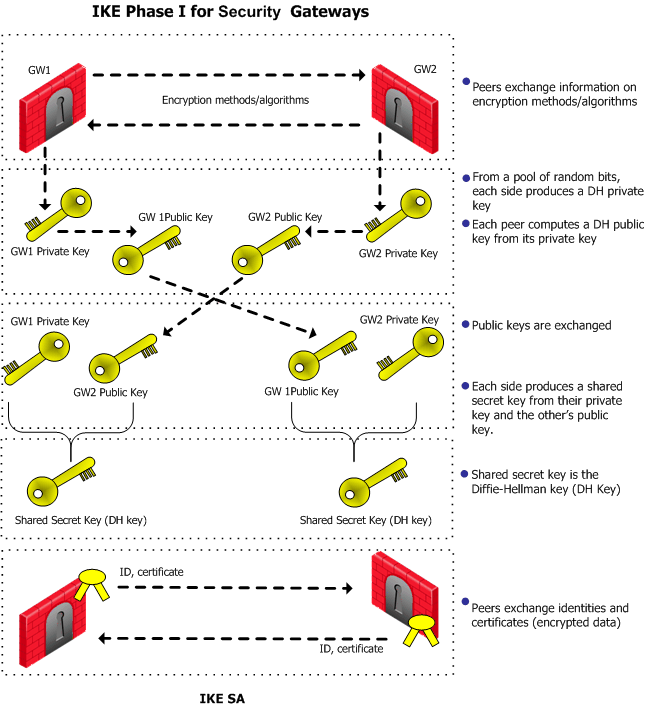
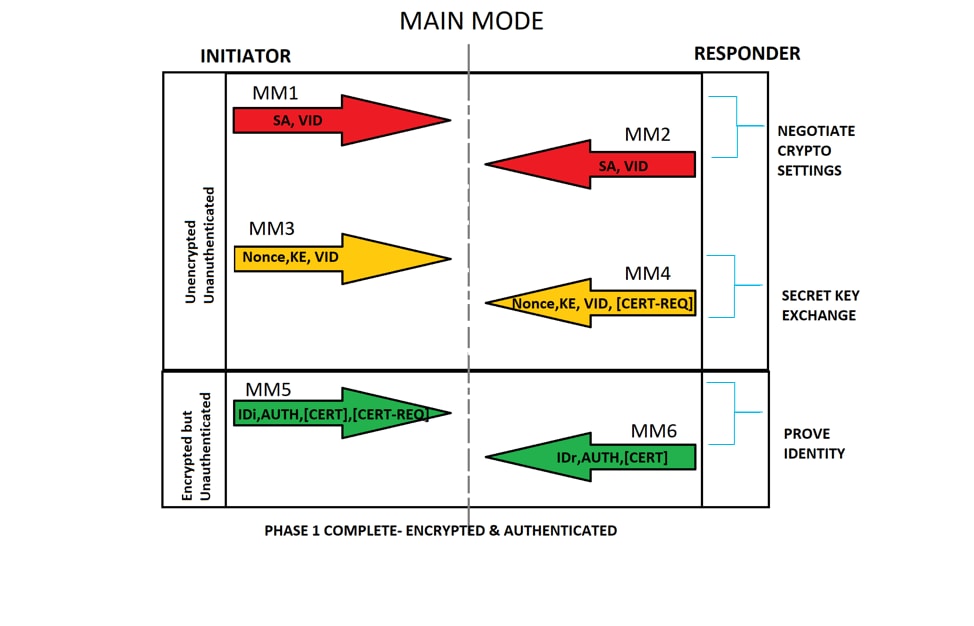
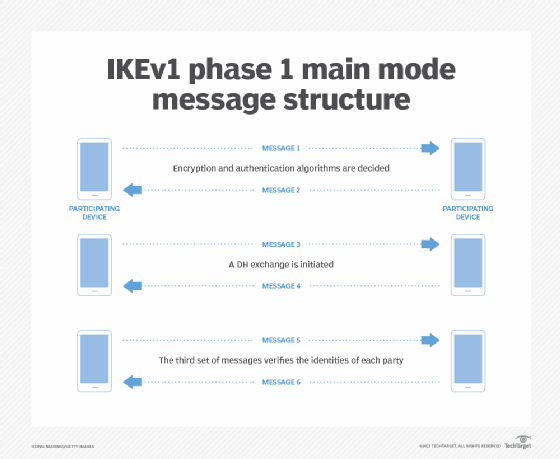
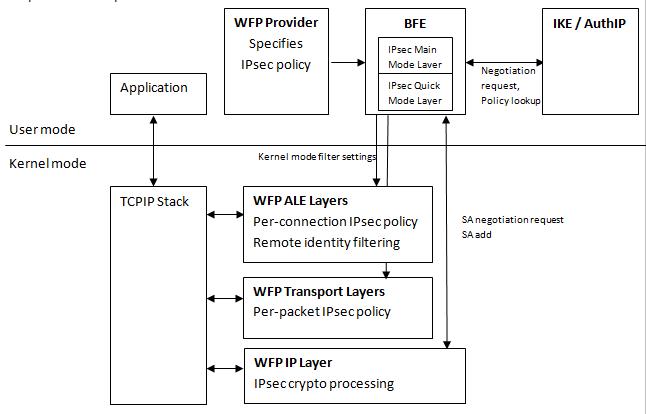
PA-VM deployed in AWS encounters IKE Phase-1 negotiation failur... - Knowledge Base - Palo Alto Networks